CVE-2017-12637: Exploitation of SAP NetWeaver Directory Traversal Vulnerability
On March 19, 2025, the CISA issued a warning about the active exploitation of CVE-2017-12637, a directory traversal vulnerability in SAP NetWeaver AS Java. This vulnerability, originally patched in 2017, has resurfaced due to incomplete mitigations, leading to increased risks for organizations using outdated or misconfigured SAP environments.
Attackers leveraging this vulnerability can read arbitrary files from the affected system, gaining access to sensitive data, including credentials stored in SAP Secure Store. This blog explores how CVE-2017-12637 is exploited, its impact, and the necessary steps to secure SAP systems.
CVE-2017-12637 – Risk Analysis
Severity: HIGH
CVSSv3.1: Base Score: 7.5 HIGH
Vector: CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:N/A:N
Exploit available in public: Yes
Exploit complexity: Low
SAP NetWeaver AS Java is a foundational platform used for running business-critical applications. The CVE-2017-12637 vulnerability arises from improper input validation in the system’s directory traversal handling, allowing attackers to access unauthorized files via a specially crafted query string in an HTTP request.
This vulnerability was initially addressed in SAP Security Note 2486657 with patches for affected versions, including:
- ENGINEAPI 7.50 SP02
- ENGINEAPI 7.50 SP03
- ENGINEAPI 7.50 SP04
- ENGINEAPI 7.50 SP05
However, in 2024, SAP released an update (SAP Note 3476549) highlighting that some systems remained vulnerable despite applying the patches. The issue stems from specific outdated components still being active, even on seemingly patched systems.
How Attackers Exploit CVE-2017-12637
- Attackers probe SAP system URLs for known vulnerabilities.
- They send HTTP GET requests with crafted path traversal sequences (../) to access sensitive system files.
- Once access is gained, attackers extract critical configuration files, credentials, or other sensitive business data.
Real-World Exploitation Trends
The Onapsis Research Labs (ORL), through its global SAP Threat Intelligence Network, has observed active exploitation of this vulnerability. Threat actors are demonstrating extensive knowledge of SAP systems, using this flaw to exfiltrate sensitive system files and escalate access to compromise entire SAP environments.
Impact of Exploitation
A successful attack leveraging CVE-2017-12637 can result in:
- Data Breach: Unauthorized access to SAP Secure Store files containing sensitive credentials.
- System Compromise: Attackers gaining privileged access to manipulate business processes.
- Regulatory Non-Compliance: Violations of GDPR, HIPAA, and PCI DSS, leading to legal and financial consequences.
- Operational Disruptions: Business-critical applications becoming targets of espionage or ransomware attacks.
Despite the CVSS v3 base score of 7.7, the impact of a successful exploit can be severe, making immediate action critical.
Mitigation and Remediation Steps
Apply the Latest Security Patches – Organizations should immediately check for and apply SAP Note 3476549 to ensure all components are fully patched.
Upgrade Outdated Components – SAP CPS 8.0 (by Redwood) has been discontinued and replaced by SAP BPA 9.0. Administrators must upgrade to BPA 9.0 using SAP Note 2278834.
Disable Unused or Vulnerable Components – For systems not requiring the ETPRJSCHEDULER component, it can be disabled using:
- SAP Note 3274660 (automatic disabling in version 750 SP27+)
- SAP Note 1592936 (manual disabling)
Implement Web Application Firewall (WAF) Protections – Deploying a WAF can help block malicious requests attempting to exploit directory traversal vulnerabilities.
Regular Security Audits and Monitoring – Continuous vulnerability scanning and threat intelligence monitoring are crucial for detecting and mitigating potential exploits before they cause damage.
AppTrana WAAP Coverage for CVE-2017-12637
AppTrana WAAP automatically defends organizations against CVE-2017-12637 exploitation attempts. With real-time threat detectiona and mitigation the platform delivers proactive security, ensuring protection from Day 0.
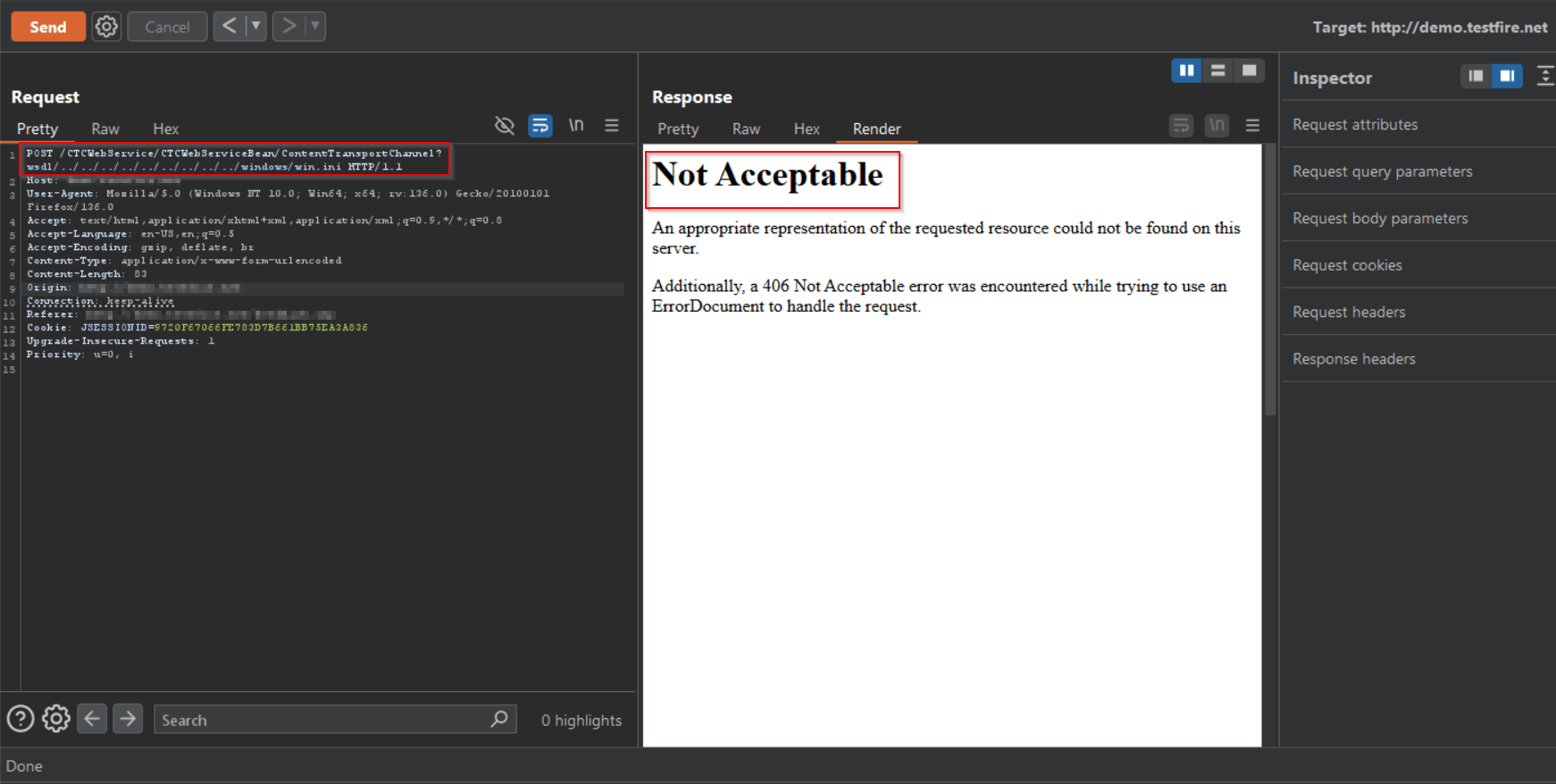
AppTrana WAAP’s core rule effectively mitigated CVE-2017-12637 exploitation attempts during proof-of-concept (PoC) simulations, as demonstrated in the screenshot.
Stay tuned for more relevant and interesting security articles. Follow Indusface on Facebook, Twitter, and LinkedIn.


 March 31, 2025
March 31, 2025



