CVE-2024-1071 – Critical Vulnerability in Ultimate Member WordPress Plugin
A critical security flaw, known as CVE-2024-1071, has been found in the Ultimate Member plugin for WordPress. This vulnerability, with a CVSS score of 9.8, poses a significant risk to over 200,000 active installations.
It potentially enables attackers to extract sensitive data from compromised databases, presenting a severe threat to website security.
Understanding the Vulnerability – CVE-2024-1071
The vulnerability affects versions 2.1.3 to 2.8.2 of the Ultimate Member plugin and revolves around an unauthenticated SQL Injection flaw associated with the ‘sorting’ parameter.
Attackers can exploit this weakness to inject malicious SQL queries, exploiting insufficient escaping mechanisms and inadequate query preparation.
Notably, users who have enabled the “Enable custom table for usermeta” option within the plugin settings are particularly vulnerable.
Active Exploitation and Threat Landscape
The severity of CVE-2024-1071 is underscored by its high-severity CVSS score of 9.8.
Notably, attackers, including the pro-Palestinian group “Handala,” are leveraging sophisticated techniques such as Time-Based blind SQL Injection to exploit this vulnerability actively.
Prevention and Mitigation
In response to the disclosure, the plugin developers promptly addressed the issue by releasing version 2.8.3 on February 19. Users are strongly urged to update their Ultimate Member plugin to the latest version promptly to mitigate potential threats.
This recommendation is crucial, given the demonstrated effectiveness of attackers in exploiting vulnerabilities within a short timeframe.
Check out the best practices to prevent SQL Injection attacks from our detailed guide.
Prior Security Incidents and Lessons Learned
This isn’t the first security incident involving the Ultimate Member plugin. In July 2023, cybercriminals exploited another weakness, identified as CVE-2023-3460, to establish unauthorized admin users and gain control of vulnerable websites. The recurrence of security challenges emphasizes the importance of robust security practices and timely software updates.
AppTrana WAAP Threat Coverage
AppTrana’s WAAP customers are shielded from this critical SQL injection vulnerability right from Day 0.
In addition to patches from the vendor, AppTrana provides additional protection patterns for an added layer of defense against potential exploits.
Our dedicated Indusface managed security team has curated rules to promptly detect WordPress plugin vulnerability and thwart attempts at exploitation.
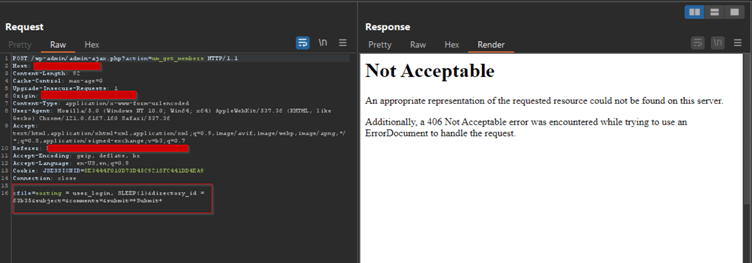
The screenshot demonstrates AppTrana WAAP’s ability to block the exploitation of this vulnerability.
WAAP instantly responds to malicious requests intercepted through Burp by delivering a robust 406-status code.
Stay tuned for more relevant and interesting security articles. Follow Indusface on Facebook, Twitter, and LinkedIn.


 March 1, 2024
March 1, 2024



