February 26, 2024
February 26, 2024 3 min Read
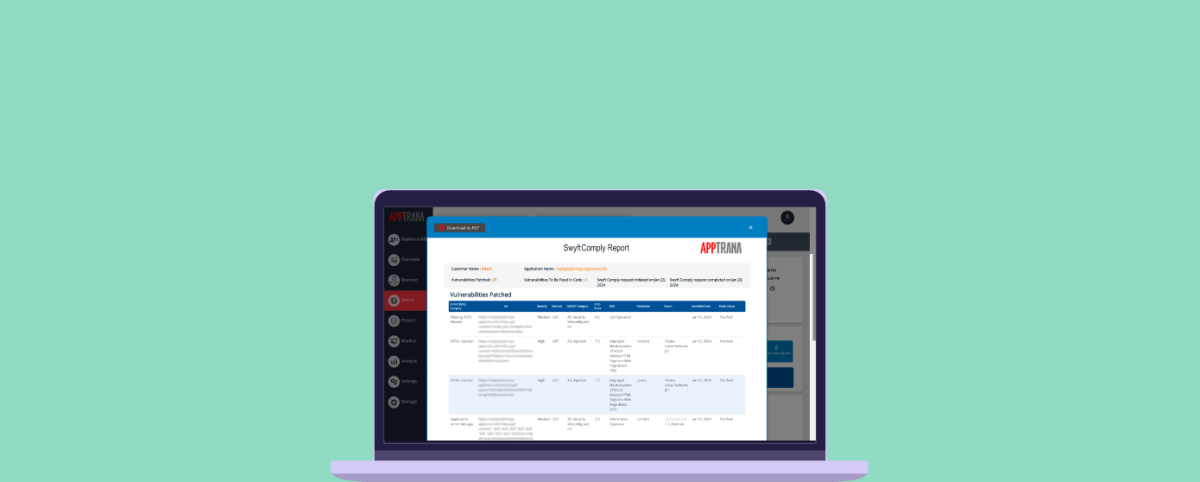
3 min ReadScreenConnect Authentication Bypass (CVE-2024-1709 & CVE-2024-1708)
Uncover critical security flaws in ConnectWise ScreenConnect (CVE-2024-1709 & CVE-2024-1708) posing remote code execution risks. Actively exploited in the wild.