Why Should Startups Endure Continuous Data Breaches?
In 1996, nine years after the launch of the World Wide Web Project, number of websites had grown…
Real-time vulnerability analysis, threat intelligence, and expert insights to protect your web, API and AI agents from emerging attacks.
In 1996, nine years after the launch of the World Wide Web Project, number of websites had grown…

Do you know about the recent bank cyber heist attempt in Bangladesh? Apparently, hackers tried to steal $951…

DROWN allows hackers to decrypt browser-server communication in hours to attack servers or/and users. Shockingly, this newly found…
Did you know that 155 .GOV and .NIC domains were hacked last year? Learn about more of such…

It’s easy to lose track of things when so much information is being shared. Indusface brings you the…
Somewhere in October, NASSCOM-DSCI closed nominations for the Excellence Award. From there, read Indusface’s journey to Emerging IS…

We bring you the top application security trends from across the world to keep the business secure.

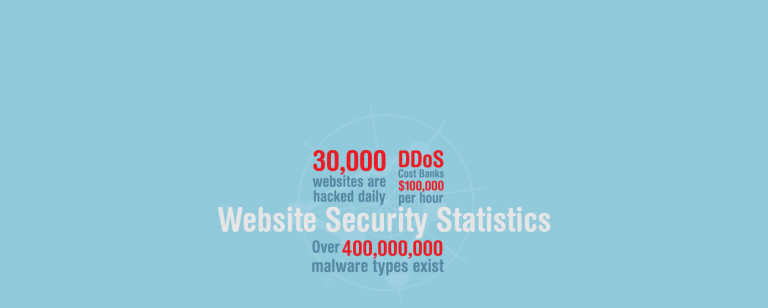
So farewell then, to 2014. This year has been a tremendous cocktail of vulnerabilities and exploitations with big…

Here are the 32 facts that you need to know about cybersecurity in 2019. Know what are the…
Data breach affects more than just data. The consequential damages will hit you for the years to come…

More than 56% cybercriminals think that winter holidays is the best time for corporate hacking. The survey was…

156 million phishing emails are received every day and a lot actually end up in the inbox. Sooner…